Zero-Knowledge Proofs: From Fundamentals to the Frontier

How to prove you know a secret without ever revealing it
Introduction
There is something almost magical about the idea of convincing someone that you know something without actually telling them what it is. No hints, no partial leaks, nothing. You walk away having proven your point, and the other person walks away fully convinced, yet completely in the dark about the underlying secret. That is, in essence, what a zero-knowledge proof is.
The concept sounds paradoxical at first. How can you prove knowledge without sharing knowledge? But this is not a thought experiment or a philosophical game. Zero-knowledge proofs (ZKPs) are a real, mathematically rigorous cryptographic tool that has grown from a niche academic curiosity in the 1980s into one of the most consequential technologies in modern cryptography. They now sit at the heart of blockchain scaling, digital identity, private transactions, and an ever-growing list of real-world applications.
This article will walk you through the fundamentals first, building up intuition with analogies before diving into the mechanics, the math, and the two major proof systems that dominate the space today. We will also look at where ZKPs are heading and why researchers think they are just getting started.
Part 1: The Basics
What Exactly Is a Zero-Knowledge Proof?
A zero-knowledge proof is a cryptographic protocol between two parties: a prover and a verifier. The prover wants to convince the verifier that a particular statement is true. The catch being, the prover must do so without revealing any information beyond the fact that the statement is indeed true.
Three properties must hold for a protocol to qualify as a zero-knowledge proof:
- Completeness - If the statement is true and both parties follow the protocol honestly, the verifier will be convinced.
- Soundness - If the statement is false, no cheating prover can convince the verifier (except with some negligibly small probability).
- Zero-knowledge - If the statement is true, the verifier learns nothing other than the fact that the statement is true. No side information leaks out.
That third property is the remarkable one. The verifier gains absolute conviction but zero additional knowledge.
The Ali Baba Cave Analogy
The most famous way to explain ZKPs is through the Ali Baba cave story, originally proposed by Jean-Jacques Quisquater and colleagues.
Imagine a circular cave with a single entrance that splits into two paths, A and B, which meet at a locked door deep inside. Peggy (the prover) claims she knows the secret word that opens the door. Victor (the verifier) wants to be convinced, but Peggy does not want to reveal the word.
Here is the protocol: Peggy walks into the cave and randomly takes either path A or path B. Victor, who stays at the entrance, does not see which path she chooses. Then Victor shouts out a request, asking Peggy to come back via either path A or path B (his choice is random). If Peggy truly knows the secret word, she can always comply. If the door is locked and she does not know the word, she can only comply when Victor happens to name the path she already took. That gives her a 50% chance of fooling Victor on any single round. But if they repeat this 20 times and Peggy succeeds every time, the probability that she is faking drops to roughly one in a million. Victor becomes convinced, yet he never learns the secret word.
This captures the spirit of ZKPs beautifully. Repetition builds confidence, randomness prevents cheating, and no secret ever crosses the boundary.
A Brief History
The concept was introduced in a 1985 paper by Shafi Goldwasser, Silvio Micali, and Charles Rackoff at MIT, titled "The Knowledge Complexity of Interactive Proof Systems." Their work showed that it is possible for a prover to demonstrate the truth of a statement without conveying any additional information. This was a groundbreaking idea, and Goldwasser and Micali went on to receive the Turing Award in 2012 for their contributions to cryptography.
Shortly after, Oded Goldreich, Silvio Micali, and Avi Wigderson published a follow-up paper demonstrating that ZKPs could be constructed for any problem in the complexity class NP. This meant the concept was not limited to a handful of toy examples but was broadly applicable across computational problems.
For decades, ZKPs remained mostly theoretical. The proofs were interactive, computationally expensive, and impractical for real systems. That changed in the 2010s, when a combination of better algorithms, more powerful hardware, and the rise of blockchain created a perfect storm of demand and capability.
Part 2: Interactive vs. Non-Interactive Proofs
Interactive Zero-Knowledge Proofs
The original ZKP formulation, and the Ali Baba cave example, involves back-and-forth communication between the prover and verifier. This is what makes them "interactive." The verifier poses challenges, the prover responds, and through repeated rounds the verifier gains confidence.
Interactive proofs are elegant and intuitive, but they have a practical limitation: both parties need to be online and communicate in real time. That is fine for academic demonstrations but does not scale well when you need to post a proof on a blockchain for thousands of nodes to verify independently.
The Fiat-Shamir Heuristic
In 1986, Amos Fiat and Adi Shamir proposed a clever transformation that converts an interactive zero-knowledge proof into a non-interactive one. The idea is surprisingly simple: instead of having the verifier supply random challenges, the prover generates those challenges themselves using a cryptographic hash function applied to the proof transcript. Because hash functions are deterministic and unpredictable, this simulates the randomness that would have come from a real verifier.
This transformation, known as the Fiat-Shamir heuristic, became the foundation for modern non-interactive zero-knowledge proofs (NIZKs). It is what makes it possible to generate a proof once and have anyone verify it later without any interaction.
Why Non-Interactive Proofs Matters
Non-interactive proofs are critical for blockchain applications. A prover can generate a proof offline, submit it to a smart contract, and every node on the network can independently verify it without needing to talk to the prover. This is what powers ZK-rollups and privacy-preserving transactions in the real world.
Part 3: Going Deeper - zk-SNARKs and zk-STARKs
This is where things get more technical. Two families of zero-knowledge proof systems dominate the landscape today, and understanding their differences matters if you want to grasp the current state of the field.
zk-SNARKs
zk-SNARK stands for Zero-Knowledge Succinct Non-Interactive Argument of Knowledge. Let us unpack each word:
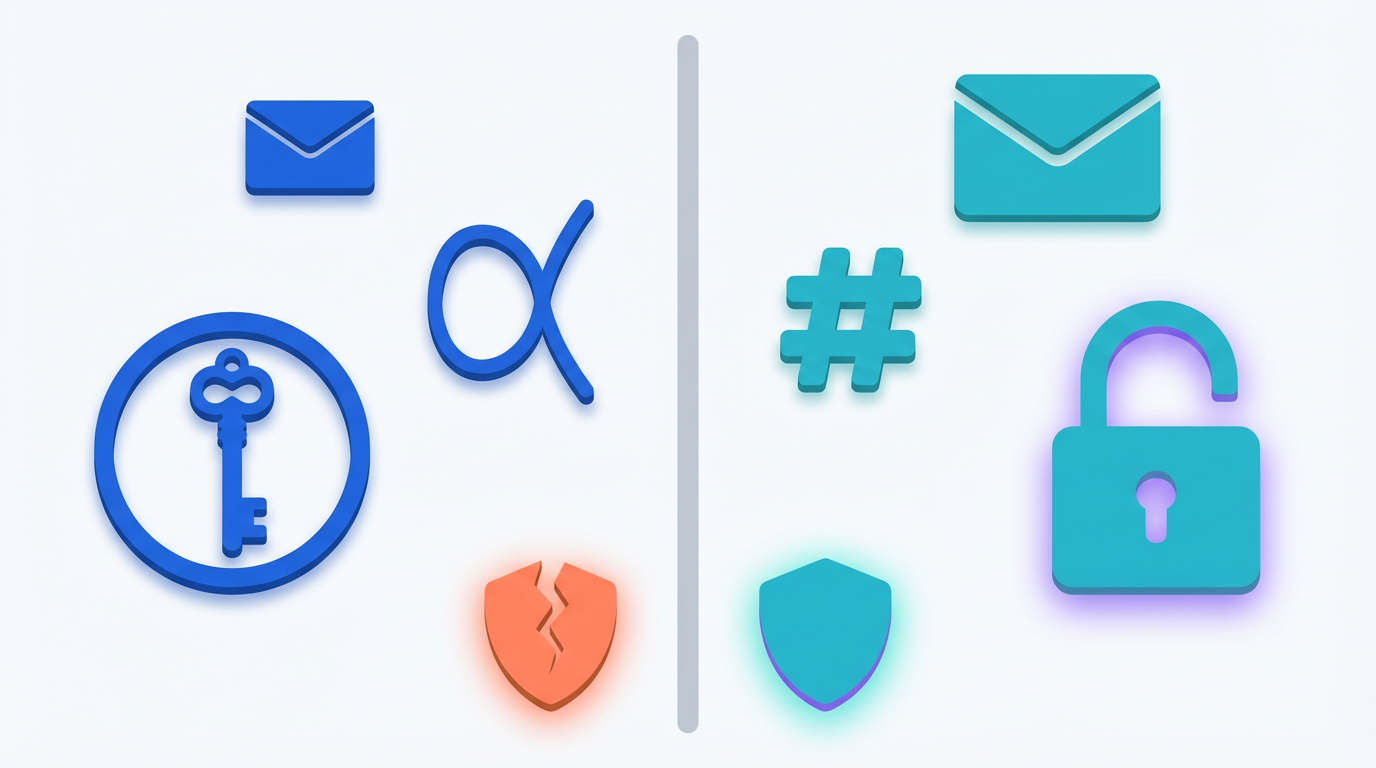
- Zero-Knowledge: The verifier learns nothing beyond the truth of the statement.
- Succinct: The proofs are small and fast to verify, regardless of the complexity of the underlying computation.
- Non-Interactive: No back-and-forth required. A single message from prover to verifier suffices.
- Argument of Knowledge: The prover demonstrates they actually possess the secret, not just that a solution exists.
The term was coined in a 2012 paper co-authored by Alessandro Chiesa at UC Berkeley. zk-SNARKs rely heavily on elliptic curve cryptography and polynomial commitments. The verification is extremely fast, often taking just milliseconds, and the proof sizes are tiny, sometimes just a few hundred bytes.
However, most SNARK constructions require a trusted setup ceremony. During this ceremony, a set of cryptographic parameters (called a Common Reference String or Structured Reference String) is generated. The process involves secret randomness that must be destroyed afterward. If anyone retains access to this "toxic waste," they could forge proof. Multi-party computation (MPC) ceremonies mitigate this risk by distributing trust across many participants, but the requirement remains a point of concern.
Another limitation is that most current SNARK schemes are not considered quantum-resistant, because they depend on the hardness of the discrete logarithm problem on elliptic curves, which quantum computers could theoretically break.
Notable projects using zk-SNARKs: Zcash (privacy coin), zkSync, Scroll, Polygon zkEVM.
zk-STARKs
zk-STARK stands for Zero-Knowledge Scalable Transparent Argument of Knowledge. First described in a 2018 paper by Eli Ben-Sasson, Iddo Bentov, Yinon Horesh, and Michael Riabzev, STARKs were designed to address some of the shortcomings of SNARKs.
Key differences:
- No trusted setup: STARKs rely on publicly verifiable randomness and collision-resistant hash functions instead of elliptic curves. There is no "toxic waste" to worry about.
- Quantum resistance: Because they use hash functions rather than elliptic curve assumptions, STARKs are considered resistant to quantum computing attacks under current cryptographic knowledge.
- Scalability: Proving and verification complexity in STARKs scale quasilinearly with computation size, compared to the linear scaling of SNARKs. For very large computations, STARKs become increasingly efficient relative to SNARKs.
STARK proofs are significantly larger than SNARK proofs. This means more data needs to be posted on-chain, which translates to higher gas costs in a blockchain context. The developer ecosystem around STARKs has also historically been smaller, though this is changing rapidly. This is the tradeoff.
Notable projects using zk-STARKs: StarkNet (by StarkWare), which uses the Cairo programming language and achieved Stage 1 decentralisation in 2025.
Head-to-Head Summary
Trusted setup: zk-SNARKs require one (in most variants), while zk-STARKs do not.
Proof size: SNARKs produce tiny proofs (hundreds of bytes), whereas STARKs generate significantly larger ones (tens to hundreds of KB).
Verification speed: Both are fast, but SNARKs have a slight edge here.
Quantum resistance: Most SNARK variants are not quantum-resistant. STARKs are, thanks to their reliance on hash functions rather than elliptic curves.
Cryptographic basis: SNARKs build on elliptic curve cryptography. STARKs build on hash functions.
Maturity: The SNARK ecosystem is more mature and widely adopted. The STARK ecosystem is catching up rapidly.
Scalability at large scale: SNARKs scale linearly with computation size. STARKs scale quasilinearly, which gives them an advantage as computations grow larger.
Part 4: How ZKPs Actually Work (A Simplified Walkthrough)
To understand ZKPs at a slightly deeper level without getting lost in the full mathematical machinery, it helps to think about the process in three stages.
Step 1: Arithmetisation
The computation you want to prove is first converted into a mathematical representation, typically a system of polynomial equations or an arithmetic circuit. This is called arithmetisation. For example, if you want to prove that you know two numbers that multiply to give a particular result, that relationship gets encoded as constraints: x * y = z.
Step 2: Polynomial Commitment
The prover then encodes the solution (the "witness") into polynomials and commits to those polynomials using a commitment scheme. This is like putting your answer in a sealed envelope. You cannot change it later, but the verifier cannot peek inside.
Step 3: Random Sampling and Verification
The verifier (or, in the non-interactive case, the hash function playing the role of the verifier) picks random evaluation points and checks whether the polynomials satisfy the required relationships at those points. If the prover's polynomials are correct, they will pass these checks. If the prover tries to cheat, the probability of passing drops dramatically with each check.
This is a simplification, of course. In practice, the details involve concepts like R1CS (Rank-1 Constraint Systems), QAPs (Quadratic Arithmetic Programs), FRI (Fast Reed-Solomon Interactive Oracle Proofs), and other deep cryptographic machinery. But the core idea is always the same: encode the computation as math, commit to your answer, and let randomness do the auditing.
Part 5: Real-World Applications
Blockchain Scaling (ZK-Rollups)
This is currently the highest-impact application of ZKPs. Ethereum and other blockchains face a fundamental bottleneck: every transaction must be verified by every node. ZK-rollups solve this by executing thousands of transactions off-chain, generating a single compact proof that the batch was processed correctly, and posting that proof on-chain. The main chain verifies one proof instead of re-executing thousands of transactions.
Ethereum's EIP-4844 (Proto-Danksharding), implemented in early 2024, introduced "blob" transactions that drastically reduced data availability costs for rollups, making ZK-rollups economically competitive. Projects like zkSync, Scroll, Polygon zkEVM, and StarkNet are all live and processing millions of transactions.
Privacy-Preserving Transactions
Zcash pioneered the use of zk-SNARKs for private cryptocurrency transactions. Users can send and receive funds without revealing the sender, recipient, or amount. The proof guarantees that the transaction is valid (no double-spending, correct balances) without exposing any details.
Digital Identity and Authentication
ZKPs enable what is sometimes called "selective disclosure." Imagine proving you are over 18 without revealing your birthdate, or proving you are a citizen of a particular country without showing your passport number. This has applications in age verification, KYC (Know Your Customer) compliance, voting systems, and access control. Projects like zkPass are exploring this space.
Verifiable Computation and AI
A newer frontier is using ZKPs to prove that a computation was performed correctly without revealing the inputs. This has significant implications for AI and machine learning. Researchers have developed protocols like "zero-knowledge proofs of training" (zkPoT) that let someone prove they trained a model correctly on a committed dataset, without revealing the model weights or the training data. The 2024 ACM CCS paper on "Kaizen" demonstrated a practical zkPoT for deep neural networks.
Supply Chain and Healthcare
ZKPs enable verification of supply chain data (product origin, quality certifications) without exposing proprietary business information. In healthcare, patient records can be verified for compliance purposes without revealing the actual medical data.
Part 6: Cutting-Edge Research
Effectively Zero-Knowledge Proofs
One of the most exciting recent developments came from Rahul Ilango at the Institute for Advanced Study in Princeton. Traditional ZKPs require the construction of a "simulator" to formally prove the zero-knowledge property. Ilango showed that in some cases, it is sufficient to simply demonstrate that a simulator's existence cannot be ruled out, even if one cannot be explicitly constructed. He drew on ideas from Godel's incompleteness theorem to build this framework. UCLA computer scientist Amit Sahai described Ilango's work as the most creative and consequential paper in the field of zero-knowledge proofs in the past decade. The result was presented at the 2025 IEEE Symposium on Foundations of Computer Science.
Under-Constrained Circuits
A 2024 systematisation of attacks found that roughly 96% of documented circuit-layer bugs in SNARK-based systems were caused by under-constrained circuits. These vulnerabilities happen when the translation from high-level logic to low-level constraint systems leaves gaps that a malicious prover could exploit. This is an active area of research, with recent work showing that formally proving "determinism" in circuits can eliminate entire classes of these bugs.
Recursive Proofs
Recursive SNARKs allow a proof to verify another proof inside itself. This creates a chain of proofs that can compress an arbitrary amount of computation into a single, constant-size proof. Projects like Mina Protocol use recursive proofs to maintain a constant-size blockchain regardless of how many transactions have occurred.
Part 7: Challenges and the Road Ahead
ZKPs are not without their challenges. Generating proofs is still computationally expensive, especially for complex circuits. The developer experience remains steep, with debugging ZK circuits being significantly harder than debugging traditional code. Specialized hardware (GPUs, FPGAs, and even custom ASICs) is being developed to accelerate proof generation, and startups like Fermah are building marketplace infrastructure to reduce costs.
Standardisation is another open problem. NIST held a Workshop on Privacy-Enhancing Cryptography in September 2024, where ZKP challenges and deployment were a central topic. The community is working toward standardizing ZK-friendly cryptographic primitives and proof systems.
Looking further ahead, the convergence of ZKPs with other technologies is opening new possibilities. ZK-rollups are evolving into interconnected ecosystems (like zkSync's "Elastic Chain" of Hyperchains). Zero-knowledge proofs are being applied to AI model verification, voting systems, and decentralized identity at scale. Ethereum's roadmap continues to prioritize ZK technology, and Vitalik Buterin has spoken repeatedly about a future where ZK proofs are deeply embedded in the protocol layer.
The field has come a long way from the theoretical papers of the 1980s. What started as a mathematical curiosity about knowledge and proof has become infrastructure, real code running on real networks, processing real transactions, and protecting real secrets.
References
- Goldwasser, S., Micali, S., & Rackoff, C. (1985). "The Knowledge Complexity of Interactive Proof Systems." Proceedings of the 17th Annual ACM Symposium on Theory of Computing (STOC)
- Goldreich, O., Micali, S., & Wigderson, A. (1986). "Proofs that Yield Nothing But Their Validity." Proceedings of the 27th IEEE Symposium on Foundations of Computer Science (FOCS).
- Fiat, A. & Shamir, A. (1987). "How To Prove Yourself: Practical Solutions to Identification and Signature Problems." Advances in Cryptology - CRYPTO '86.
- Ben-Sasson, E., Bentov, I., Horesh, Y., & Riabzev, M. (2018). "Scalable, Transparent, and Post-Quantum Secure Computational Integrity." IACR Cryptology ePrint Archive.
- Chiesa, A. et al. (2012). The paper coining the term "zk-SNARK." UC Berkeley.
- Ilango, R. (2025). "Effectively Zero-Knowledge Proofs." Presented at the 2025 IEEE Symposium on Foundations of Computer Science, Sydney.
- ACM CCS 2024. "Zero-Knowledge Proofs of Training for Deep Neural Networks" (Kaizen).
- NIST WPEC 2024. "Zero Knowledge Proofs: Challenges, Applications, and Real-world Deployment." Silde, T. & Takahashi, A.
- Chainlink Education. "Zero-Knowledge Proof (ZKP) Explained." https://chain.link/education/zero-knowledge-proof-zkp
- Consensys. "Zero-Knowledge Proofs: STARKs vs SNARKs." https://consensys.io/blog/zero-knowledge-proofs-starks-vs-snarks
- CoinGecko. "What Are Zero-Knowledge Proofs and ZK-Rollups?" https://www.coingecko.com/learn/zero-knowledge-proofs-and-zk-rollups
- Scientific American. "How 'Effectively Zero-Knowledge' Proofs Could Transform Cryptography." (2025) https://www.scientificamerican.com/article/how-effectively-zero-knowledge-proofs-could-transform-cryptography/
- Communications of the ACM. "The Power and Potential of Zero-Knowledge Proofs." (July 2025) https://cacm.acm.org/news/the-power-and-potential-of-zero-knowledge-proofs/



